Abstract Security Threat Research Organization · 2025–2026
PRICED TO MOVE
The Underground Markets of Modern Cyberattacks
15 threads
372 posts
5 researchers
|
[Staff]
Sherlog Holmes

Researcher
ASTRO
Posts:847
Threads:156
Reputation:88
|
Intrusion is now industrialized. A mature market of Initial Access Brokers (IABs) now supplies pre-compromised footholds into enterprise networks, allowing ransomware and extortion groups to skip reconnaissance and move directly to monetization. By specializing in the initial access phase and selling unauthorized access to compromised networks, IABs have lowered the barriers to entry for sophisticated cyberattacks, making them faster, more scalable, and alarmingly efficient. Modern intrusions increasingly rely on compromised credentials rather than exploit chains. Valid accounts (particularly those without multi-factor authentication) have become the dominant entry vector. At the same time, the rapid expansion of SaaS platforms alongside legacy VPN and on-premise infrastructure has created a dispersed identity surface that is difficult to inventory comprehensively and even harder to monitor in real time. IABs operate within this fragmentation. By harvesting, validating, and reselling authenticated access across hybrid environments, they convert configuration gaps and visibility blind spots into tradable entry points. Analysis of 2025 data reveals that the ransomware threat has intensified dramatically, with attack volumes surging 47% compared to the prior year while average costs to acquire network access have plummeted to unprecedented lows. [1,8] This research reflects ongoing monitoring conducted by the Abstract Security Threat Research Organization (ASTRO), including longitudinal tracking of active IAB operators and correlation of credential abuse and CVE exploitation patterns. Key Findings
Primary Entry Vectors: Q1 2025 Percent of Incidents [2,4]
Valid Accounts (No MFA)56%
Other Vectors44%
↑ Credential abuse has displaced vulnerability exploitation as the dominant entry
method.
Identity-Related Root Causes: 2025 Incidents [33]
Identity-Related67.3%
MFA Absent/Misconfigured~60%
Source: Sophos 2026 Active Adversary Report
Access Broker Activity: Year-over-Year [34]
Stolen Credential Ads (2024)baseline
Stolen Credential Ads (2025)+50% ▲
Source: CrowdStrike 2025 Global Threat Report
IAB Listing Composition: What's Being Sold [2]
VPN Access23.5%
Domain User Accounts19.9%
RDP Access16.7%
Other39.9%
Include Elevated Privileges71.4%
↑ Bundled access packages with domain admin, multiple entry points, or privileged
accounts.
Dwell Time Compression [4,17]
Typical (Early 2024)9–11 days
Q4 2024 Median5 days
Fastest Observed<24 hrs
Execution speed is accelerating — median time from initial access to ransomware
halved in 2024.
Sector Targeting: Year-over-Year Attack Volume [6]
Healthcare+600% ▲
Government+65% ▲
EducationHighest Volume
Education recorded the highest overall attack volume; Healthcare saw the largest
growth rate.
Critical Threats for 2026The ecosystem demonstrated remarkable resilience despite law enforcement successes: BreachForums returned months after its April 2025 takedown [31], and 57 new ransomware groups emerged to fill gaps left by disrupted operations. [8] Intelligence assessments predict 2026 will mark the first year that non-Russian ransomware actors will outnumber those within Russia. [1,9] An alarming trend of ransomware groups recruiting corporate insiders further blurs the line between external and internal threats. [13] Primary RecommendationsImmediate (0–30 days):
Near-Term (90–180 days):
Long-Term Resilience:
Scope and MethodologyThis paper synthesizes findings from Rapid7's 2025 Access Brokers Report [2], Recorded Future's ransomware tracking [1], Check Point's 2026 Cyber Security Report [9], Cyble's ransomware group analysis [8], and incident response data from Arctic Wolf, Sophos, and other leading vendors. [4,17] Complementing the landscape analysis, this paper incorporates original threat research conducted by ASTRO, based on 12 months of continuous monitoring of a specific volume-based IAB operator (Section 6). This ground-level data—including credential analysis across 30,000+ compromised devices and temporal correlation between CVE proof-of-concept releases and exploitation surges—provides empirical validation of the trends and defensive recommendations described throughout. |
|
[Staff]
Sherlog Holmes

Researcher
ASTRO
Posts:847
Threads:156
Reputation:88
|
On an otherwise unremarkable day, an attacker known as ToyMaker, tracked by researchers as GoldMelody and UNC961, exploited known vulnerabilities in an internet-facing server belonging to a critical infrastructure enterprise. The intrusion itself was methodical. ToyMaker deployed a custom backdoor called LAGTOY, a reverse shell implant that persisted as a Windows service named "WmiPrvSV" and communicated with a hardcoded command-and-control server over TCP port 443, a port that blends seamlessly with normal HTTPS traffic. Within the first week, ToyMaker enumerated users, created a rogue administrator account named "support," extracted credentials using Magnet RAM Capture, and exfiltrated the memory dump via PuTTY's SCP utility. Then... nothing. For approximately three weeks, the network sat untouched. ToyMaker made no attempt to steal data. They did not pivot to high-value systems and they did not deploy ransomware. The sole objective was to package what they had found and sell it. After the three-week gap, the Cactus ransomware group entered the network using the credentials ToyMaker had harvested. Cactus deployed its own entirely independent tooling (PowerShell remoting scripts for enumeration, 7-Zip for compression, curl for exfiltration) before detonating ransomware across the environment. The entire chain, from ToyMaker's initial exploitation to Cactus's deployment, spanned roughly five weeks. [36] But the three-week silence was not inactivity. It was a transaction. 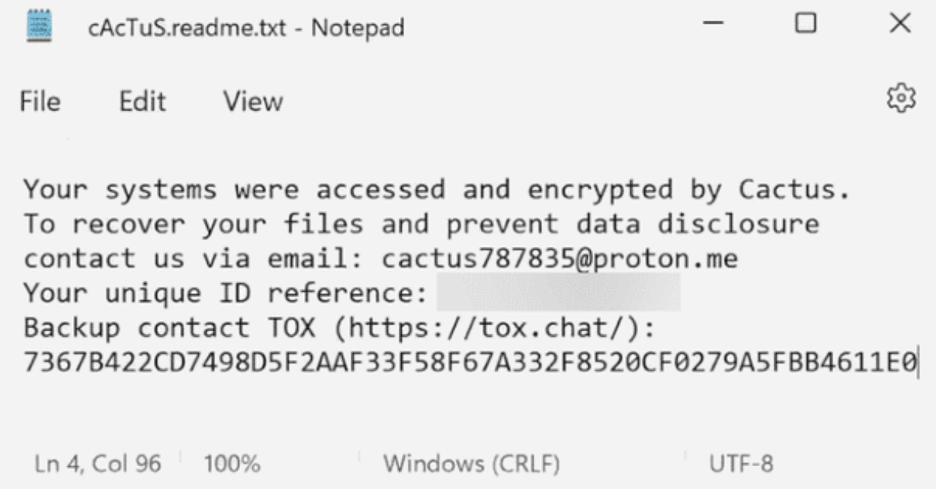
Figure 1: cAcTuS.readme.txt
1.1 GoldMelody/UNC961: Technical Deep-DiveActive from October 2024 through March 2025, GoldMelody represents the upper tier of IAB sophistication. The group deployed in-memory IIS modules and exploited leaked ASP.NET machine keys to maintain stealthy persistence, techniques suggesting possible state-affiliated connections. [12]
Technical DetailsThe group exploited leaked ASP.NET machine keys hardcoded in web.config files, enabling arbitrary code execution on IIS servers. Custom C++ IIS modules were loaded directly into w3wp.exe memory, providing backdoor access and credential harvesting without writing malicious files to disk, evading signature-based detection. A binary named "updf" masqueraded as a PDF utility but performed Windows privilege escalation. The group made extensive use of living-off-the-land techniques: net.exe, nltest.exe, whoami.exe, PowerShell AD cmdlets. A consistent staging directory at C:\Windows\Temp\111t was used across multiple intrusions. Indicators of Compromise
Disruption OpportunitiesThe three-week gap between initial compromise and ransomware deployment represents a detection window that most organizations struggle with. During that window, ToyMaker's activity generated multiple observable signals: a new local administrator account created outside of change management, memory dumping tools executing on production servers, SCP-based data exfiltration from unexpected processes, and a Windows service installed with a name mimicking a legitimate WMI component. Any one of these indicators, if detected and investigated, would have broken the attack chain before Cactus ever gained entry. [36] Lessons Learned
![IAB listing on exploit[.]in forum showing target attributes, access type, and pricing](https://cdn.prod.website-files.com/69847dcdf15f603ba59220d8/69b219971b5b8fa9bf06fb06_exploit_forums_seller4.png)
Figure 2: IAB listing on exploit[.]in forum showing target attributes, access type,
and pricing.
|
|
[Staff]
Sherlog Holmes

Researcher
ASTRO
Posts:847
Threads:156
Reputation:88
|
ToyMaker did not behave like a traditional hacker. They breached a network, packaged what they found, and sold it. That transaction is the defining feature of Initial Access Brokers. 2.1 The Evolution of Cybercrime SpecializationOver the past decade, cybercrime has reorganized into a segmented economy. Distinct actors now specialize in narrow functions across the intrusion lifecycle and sell those capabilities to one another. Malware developers maintain and lease payloads through Ransomware-as-a-Service (RaaS) platforms. Bulletproof hosting providers sell infrastructure designed to withstand takedown attempts. Exploit developers monetize newly discovered vulnerabilities. Negotiators manage ransom payments. Access sellers source and resell footholds into corporate networks. Each role focuses on a specific operational task, increasing efficiency through repetition and scale. Capabilities that once required a single actor to possess reconnaissance skill, exploit development expertise, lateral movement tradecraft, and monetization channels are now distributed across participants who optimize for one layer of the workflow. 2.2 What Are Initial Access Brokers?+--------------------------------------------------------------+ | INITIAL ACCESS BROKER (IAB) OPERATION MODEL | +--------------------------------------------------------------+ +------------------+ +------------------+ +------------------+ | 1 IDENTIFICATION |-->| 2 EXPLOITATION |-->| 3 VALIDATION | | | | | | & PRIV ESCAL. | +------------------+ +------------------+ +---------+--------+ ________________________________| | v +---------+--------+ +------------------+ | 4 LISTING |-->| 5 TRANSACTION | | | | | +------------------+ +------------------+ Initial Access Brokers (IABs) are specialized cybercriminals who concentrate on a singular objective: gaining unauthorized entry into computer systems and corporate networks, then selling that access to other malicious actors. Unlike traditional hackers who exploit access for direct gain, IABs treat network intrusion as a product, and they breach, package, and sell access as a commodity on underground marketplaces. The IAB business model operates through five distinct phases:
2.3 Why IABs Matter Now: The 2025 Inflection PointThree converging factors define why IABs demand immediate attention. First, ransomware attack volumes surged to 7,200 publicly reported incidents in 2025, a 47% increase, even as median ransom demands dropped to $217,000. [3,16] IABs enable this volume strategy: with access available for under $1,000, operators can target dozens of victims simultaneously. Second, IABs have democratized sophisticated cyberattacks by eliminating the skill barrier. Bundled access packages with domain admin credentials let unsophisticated actors launch attacks that previously required advanced capabilities. Third, the IAB marketplace has increasingly attracted nation-state actors, with groups like GoldMelody/UNC961 demonstrating dual financial and state-affiliated motivations, blurring the line between cybercrime and espionage. [12] |
|
[Analyst]
Anna Lies

Market Analyst
ASTRO
Posts:312
Threads:67
Reputation:54
|
The IAB marketplace operates as a sophisticated underground economy with transparent pricing, quality guarantees, and standardized service levels. 3.1 Market Size and Underground MarketplacesThe IAB market reached a minimum valuation of $6.3 million in 2024 based on publicly advertised prices across major forums. [15] The total revenue of organizations listed for sale exceeded $3 trillion. Growth has been explosive: IAB listings increased 147% from 2022 to 2023 [14], ransomware attacks grew 47% from 2024 to 2025 [1,8], 57 new ransomware groups emerged in 2025 [8], and access-for-sale listings in the top 10 targeted countries grew 90%. [15] IABs primarily operate through four major dark web forums:
Forums implement escrow services (5–10% fee), reputation systems with verified seller badges, proof-of-access requirements, and replacement guarantees (24–72 hours) to professionalize transactions and reduce buyer friction. [14,15] ![Figure 3: The Exploit[.]IN dark web forum,](https://cdn.prod.website-files.com/69847dcdf15f603ba59220d8/69b223ea42b7f51147511ef2_ExploitForums.png)
Figure 3: The Exploit[.]IN dark web forum, one of the primary IAB marketplaces.
3.2 Pricing DynamicsThe 2025 IAB market demonstrates clear pricing stratification with a dramatic shift toward affordability:
Average sale price: $2,700. The defining trend of 2024–2025 is the shift toward volume: 58% of listings fell under $1,000 (up from ~40% in 2023), and 86% under $3,000. High-value listings (>$10,000) declined from ~15% to 7%. [14] Price Band Concentration: Share of Listings
Under $1,000
2023~40%
2024+58% ▲
Under $3,000
2024+86%
Over $10,000
2023~15%
2024+7% ▼
↑ Dramatic shift toward volume pricing. Access is cheaper and more abundant than
ever.
Key pricing factors include organization revenue, access type (domain admin credentials command 2–5x premiums over standard user access), industry sector, security posture (absence of MFA and presence of only Windows Defender increase value), and geography (US targets represent 31–48% of listings and command 20–30% premiums). [2,15] 3.3 The IAB-Ransomware ConnectionIABs and ransomware operations have evolved from transactional relationships into integrated partnerships. Many IABs maintain standing relationships with specific RaaS operations, receiving flat rates or revenue-sharing arrangements (typically 10–20% of ransom) rather than per-access fees. This symbiosis drives attack acceleration: median dwell time from initial access to ransomware deployment dropped to just 5 days in Q4 2024, down from 9–11 days earlier in the year. [4,17] Some attacks achieved deployment in under 24 hours. [1] The economics are compelling: with access priced at $500–$1,000, ransomware operators can launch simultaneous campaigns across dozens of targets. When 71.4% of purchases include elevated privileges, operators can begin lateral movement immediately without spending time on privilege escalation. [2] 3.4 Geographic Targeting [2,14,15]
3.5 Industry Sectors [2,6,14,15,27,29]
3.6 Organization Size
The shift toward mid-market ($5M–$50M) organizations reflects the volume strategy: these organizations typically lack dedicated security teams, operate with constrained IT budgets, often use only Windows Defender, and represent the "Goldilocks zone", valuable enough to pay moderate ransoms but not so large they can rebuild from backups. [14,15] |
|
[Staff]
Sherlog Holmes

Researcher
ASTRO
Posts:847
Threads:156
Reputation:88
|
The IAB landscape includes operators ranging from opportunistic credential sellers to sophisticated actors with potential nation-state connections. Understanding the tiers helps defenders prioritize and helps analysts attribute activity correctly. You already know Tier 1, that was ToyMaker. 4.1 Operational TiersTier 1 (Elite): Operators like GoldMelody/ToyMaker develop custom tooling, target high-value organizations, and maintain extended access before sale. Minimal public forum presence; direct RaaS relationships. Pricing $5K–$50K+. Weeks to months of dwell time. Comprehensive intelligence packages. Tier 2 (Professional): Actors like SGL and IntelBroker balance sophistication with volume. Established forum reputations, consistent quality. Pricing $1K–$10K. Days to weeks of dwell time. Tier 3 (Opportunistic): Operators like Br0k3r rely on automated scanning and purchased info-stealer logs. High volume, rapid turnover, minimal post-compromise activity. Pricing $200–$2K. Hours to days from compromise to listing. 4.2 Notable IAB Operators
|
|
[Researcher]
ZeroDayZen

Exploit Researcher
ASTRO
Posts:203
Threads:41
Reputation:71
|
IAB operations follow predictable patterns driven by economic efficiency and technical feasibility. Understanding these TTPs enables defenders to identify and disrupt IAB activity before access reaches ransomware operators. 5.1 Initial Access Methods
IAB Sales figures from [2,14,15]; Attack percentages from [33,34,35]; Trend characteristics from [1,9]
VPN Compromise: The Rising ThreatVPN access surged to become the most common IAB offering (23.5% in 2025, more than doubled from 2023). [2] VPN access typically comes with working credentials and no MFA, allowing attackers to blend with legitimate traffic. Multiple high-profile VPN platforms experienced critical vulnerabilities in 2024–2025, including Fortinet FortiOS (CVE-2024-21762, CVE-2024-55591), Ivanti products (CVE-2024-21887, CVE-2026-1281), and SonicWall SSL VPN. IABs also increasingly purchase stolen VPN credentials from info-stealer operators rather than exploiting technical vulnerabilities. [4,32] 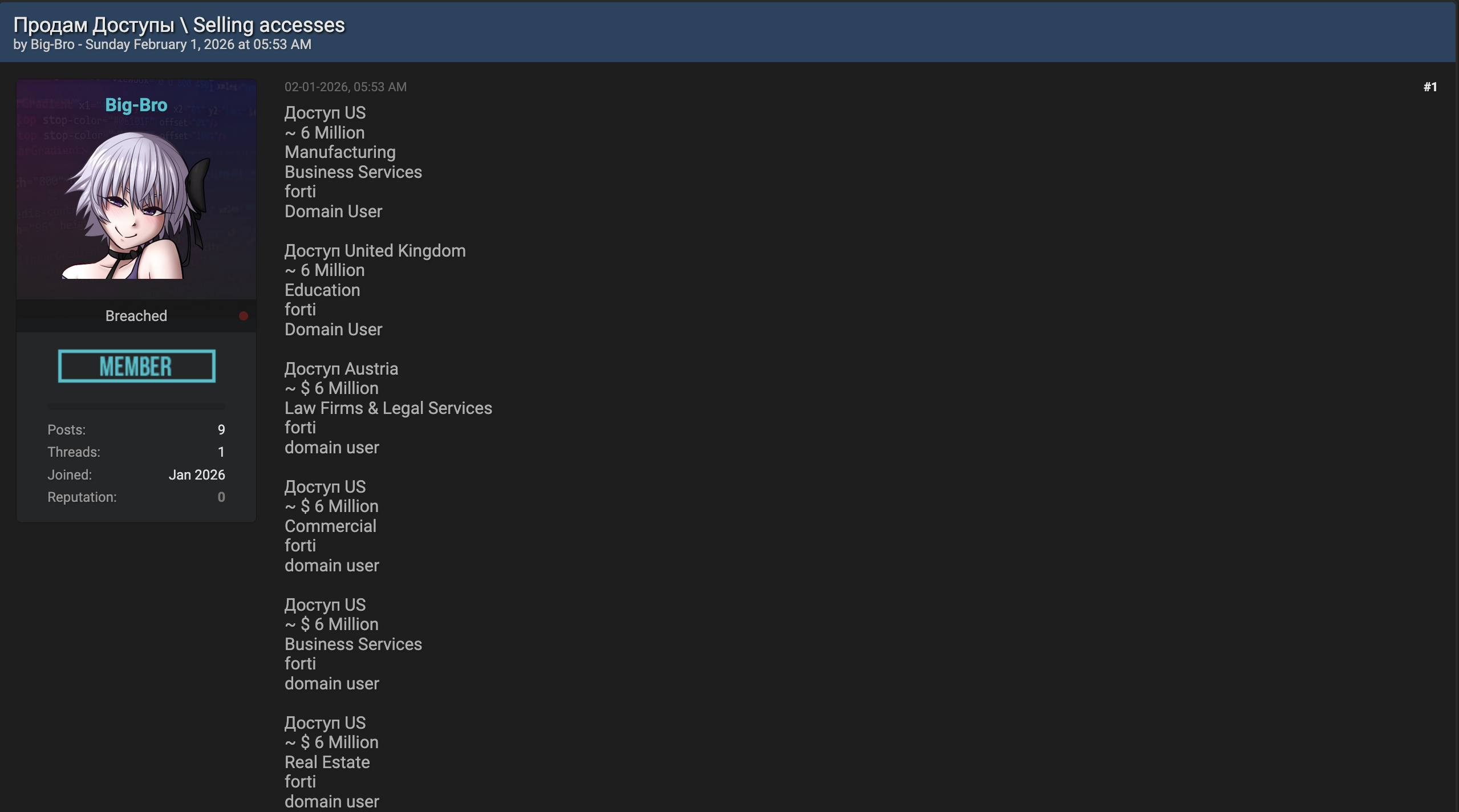
Figure 4: IAB on breachforums[.]as selling multiple network accesses across different
countries and industries.
The Credential Abuse ShiftThe most significant tactical evolution in 2025 is the shift from vulnerability exploitation to credential-based access. At 56% of Q1 2025 incidents, valid accounts without MFA represent the single most common initial access vector. [2,4] This shift lowers technical barriers, evades detection (valid credentials bypass signature-based detection and EDR), and reflects the growing info-stealer ecosystem where malware operations like Raccoon Stealer, RedLine, Lumma, and Vidar feed credentials to IABs who in turn supply ransomware operators. [1,10] 5.2 Common Vulnerabilities ExploitedWhile credential abuse dominates, vulnerability exploitation remains significant at 32% of attacks. Original tracking data from ASTRO (Section 6) demonstrates a direct temporal correlation between PoC release dates and exploitation surges by opportunistic IABs.
|
|
[Staff]
Sherlog Holmes

Researcher
ASTRO
Posts:847
Threads:156
Reputation:88
|
The preceding sections draw from published threat intelligence. This section presents original research conducted by ASTRO, based on 12 months of continuous monitoring of a specific IAB operator — a ground-level view of how a Tier 3 (opportunistic) broker operates at industrial scale. This operator was tracked from November 2024 through February 2026. 6.1 Operator ProfileThis IAB specializes in compromised VPN appliances across three vendors: Cisco ASA, Palo Alto GlobalProtect, and Fortinet FortiGate. Their primary method is automating credential spraying against internet-facing VPN management interfaces using default or near-default credentials. The operator is purely opportunistic — no filtering of industry, revenue, or geography. The victim pool ranges from 15-host small businesses to networks with thousands of endpoints belonging to major enterprise subsidiaries. Every listing from this operator follows a standardized template: VPN credentials with external IP and port, internal network range, domain controller IP, and host count. No security product inventory, no backup system mapping, no lateral movement scripts. Compare this to GoldMelody (Section 1), who spends weeks on reconnaissance and provides comprehensive intelligence packages. This operator's recon takes minutes and fits an index card — but the volume is what makes it dangerous. Pricing follows Tier 3 norms: $200–$2,000 per listing depending on host count and perceived organization size. 6.2 Credential AnalysisAnalysis of the credential pairs used across the full tracking period reveals the scale of the configuration hygiene failure enabling this operator. The most common combination, user:user, was found on nearly 30,000 unique devices. Other high-frequency pairs include test:password (25,000+), user:12345678 (18,000+), and SSLVPN1:SSL@user#2025 (18,000+). Several patterns emerge. First, vendor-specific defaults are well represented: cisco:password appears in the top 10, and the SSLVPN1 credential is specific to Fortinet SSL VPN test accounts, suggesting appliances deployed with factory settings and never hardened. Second, the long tail of credentials includes what appear to be real personal names, suggesting legitimate user accounts with weak passwords, indicating organizations where password policies are absent or unenforced. Third, the credential user@sslvpn:s3@!89fg%$&ssjd appears superficially complex but was found on over 5,000 devices, suggesting it may be a widely shared deployment template credential that administrators assumed was unique. 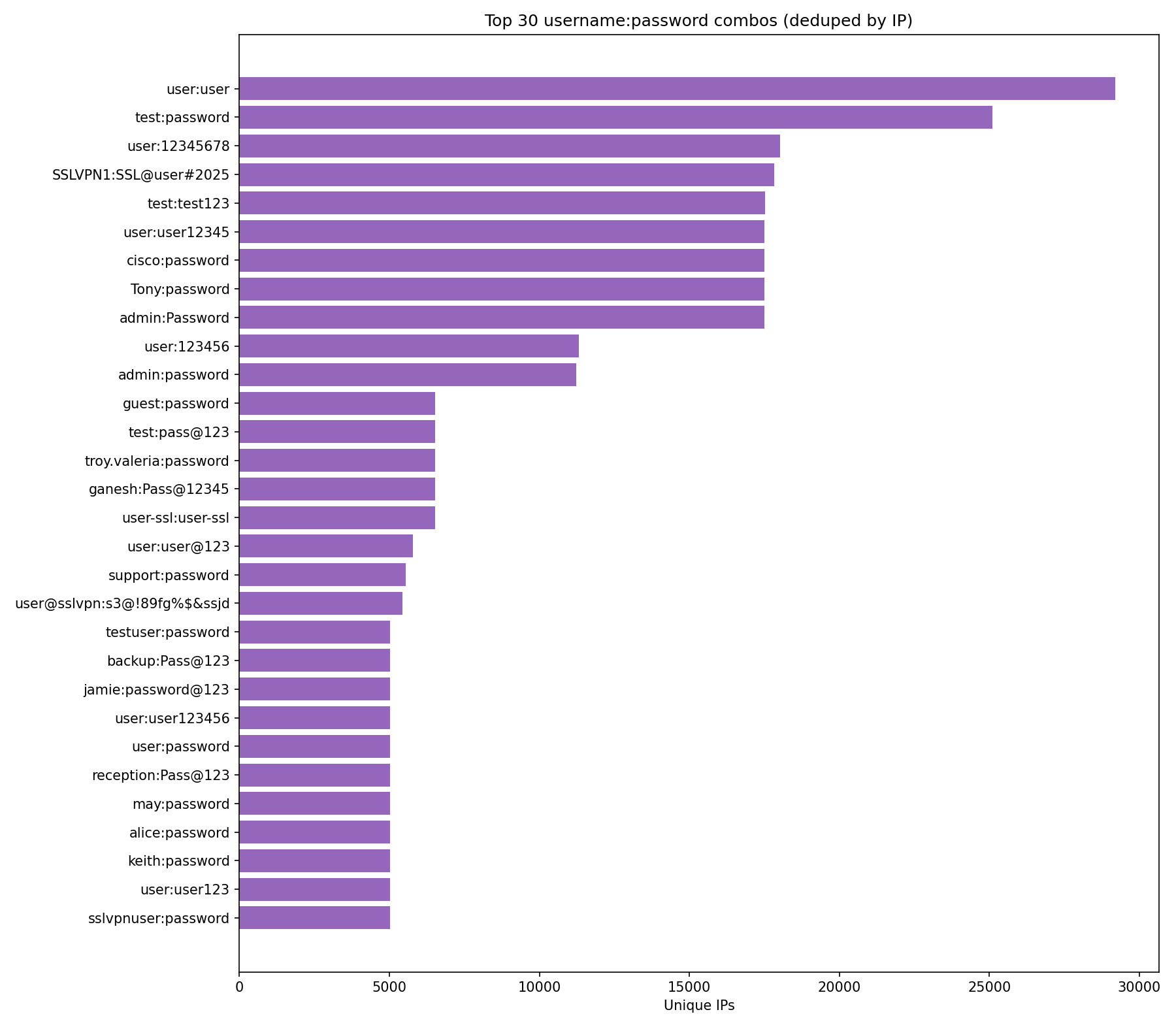
Figure 5: Top 30 username:password combinations observed from tracked IAB operator,
deduplicated by unique IP. Default and trivial credentials dominate, with user:user
found on nearly 30,000 devices.
6.3 CVE Exploitation CorrelationWhile credential spraying forms this actor's baseline activity, the tracking data reveals a clear pattern of rapid pivoting to newly disclosed vulnerabilities. In October 2024, Cisco disclosed a batch of critical ASA vulnerabilities. Six to eight weeks later (the typical patch reverse-engineering time) the Cisco line spiked to approximately 17,700 unique compromised IPs in December 2024. The most dramatic correlation appears with CVE-2025-32756, a Fortinet stack-based buffer overflow (CVSS 9.8) with proof-of-concept code released in late May 2025. Within six weeks, the Fortinet compromise count surged from approximately 400 to over 20,000 unique IPs, peaking at 23,000+ in September–October 2025 before dropping sharply in November, likely reflecting mass patching finally outpacing exploitation. This demonstrates how an operator with scanning infrastructure already in place can weaponize a new CVE across the entire internet-facing attack surface within weeks, if not days. 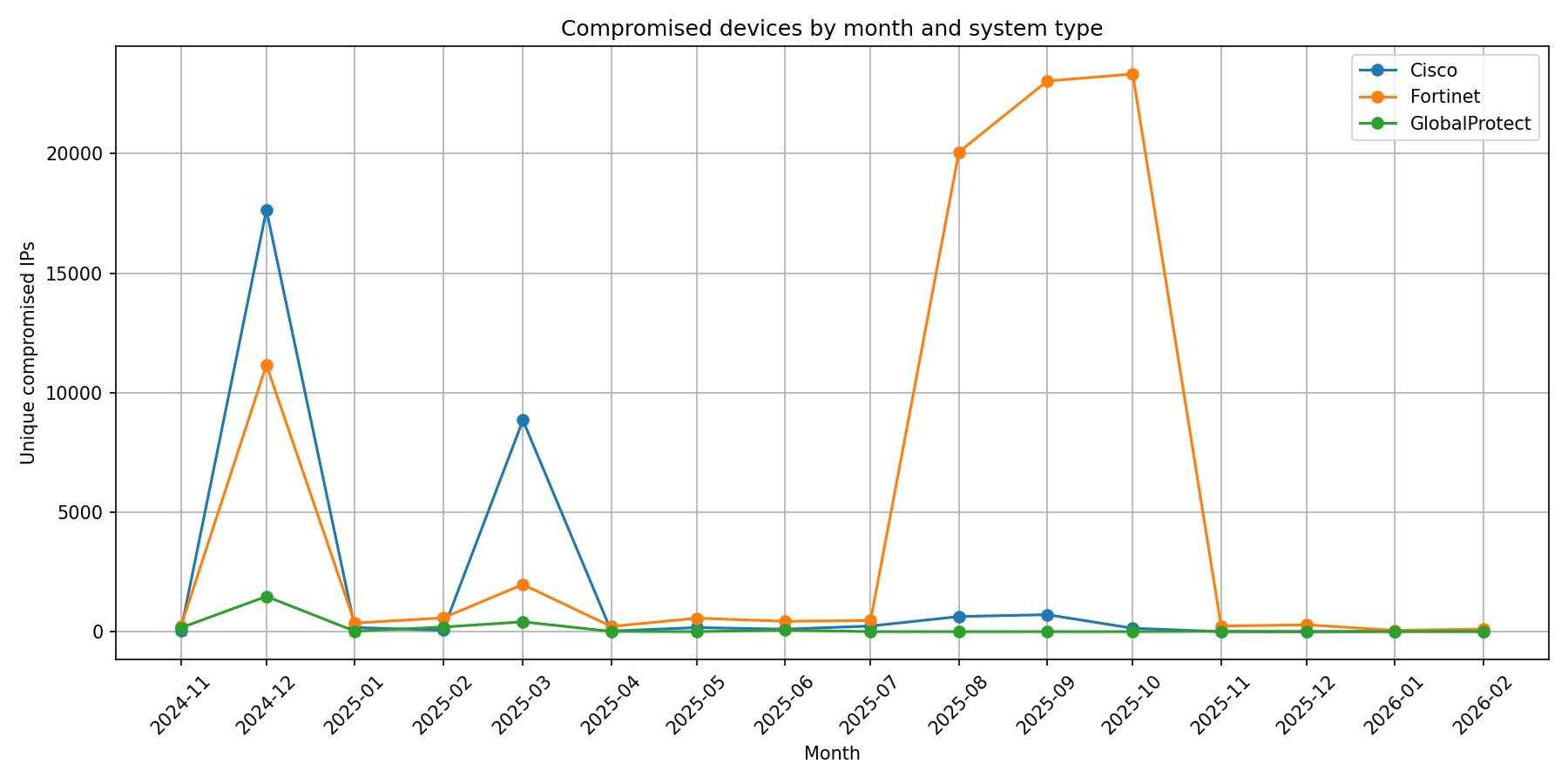
Figure 6: Compromised devices by month and vendor, with CVE PoC release dates
overlaid. The Cisco October 2024 batch correlates with the December 2024 spike;
CVE-2025-32756 correlates with the July–October 2025 Fortinet surge.
6.4 Key Findings
|
|
[DFIR]
Abby Stract

Incident Responder
ASTRO
Posts:276
Threads:52
Reputation:59
|
Note: This composite case study is constructed from multiple documented incidents and publicly reported data to illustrate a typical IAB-to-ransomware pipeline. Individual details are drawn from real-world events; the specific organization and financial figures are representative. A US healthcare organization with $45M in annual revenue. 450 workstations, 75 servers. Windows Defender only. Backups accessible from the production network. No MFA on VPN. On July 15, an employee clicked a malicious ad, downloaded trojanized software containing RedLine Stealer, and their VPN credentials were harvested from the browser. An IAB validated the access over the following week, mapping the network, noting the security posture. On July 26, a listing appeared on XSS forum: "US Healthcare | $45M revenue | VPN + Domain User | Defender only | Backups accessible | $2,500." The access sold for $2,200 the next day.
7.1 Financial Impact
Table 7.1: Composite financial impact based on industry benchmarks [4, 17, 25, 26, 30]
|
|
[OSINT]
Dr. Detector

OSINT Analyst
ASTRO
Posts:189
Threads:38
Reputation:62
|
The June 2025 unsealing of charges against IntelBroker (Kai Logan West) demonstrates how operational security failures enable law enforcement attribution despite sophisticated anonymization practices. This case provides the most detailed public account of successful IAB identification to date. [20] 8.1 BackgroundKai Logan West, a 25-year-old British national, operated as IntelBroker from approximately December 2022 through February 2025. During that period, he offered stolen data for sale at least 41 times and distributed it freely or for forum credits approximately 117 more times across BreachForums, causing over $25 million in documented damages to more than 40 victim organizations worldwide. [20] His targets included Cisco, AMD, Zscaler, Hewlett-Packard Enterprise, Europol, and DC Health Link. [22,23] From August 2024 through January 2025, West served as the owner of BreachForums itself. [24] In an ironic detail revealed during the investigation, West had previously worked as a trainee at the UK's National Crime Agency, the very agency that cooperates with the FBI on cybercrime investigations. [23] 8.2 The Investigative BreakthroughIntelBroker typically insisted on payment in Monero, a privacy-focused cryptocurrency resistant to blockchain analysis. The investigation's critical break came in January 2023 when an undercover law enforcement officer, posing as a buyer, successfully convinced IntelBroker to accept Bitcoin instead of Monero for a controlled purchase of stolen data. The Bitcoin address IntelBroker provided enabled a chain of attribution that unraveled his entire identity. [21] Using Chainalysis Reactor, investigators traced cryptocurrency flows from IntelBroker's Bitcoin address to an account on the Ramp cryptocurrency exchange. Ramp's KYC records revealed the account was registered to "Kai Logan West," verified with a UK driver's license, the first concrete connection between the IntelBroker persona and a real-world identity. [20,21] Additional corroboration: the same IP addresses were used for both West's personal activities and IntelBroker's forum operations. [22] West viewed YouTube videos covering his own breaches from his personal IP, then the IntelBroker account posted those same videos on BreachForums. [23] 8.3 Arrest and ChargesFrench authorities arrested West at his residence in France in February 2025. The US Attorney for the Southern District of New York unsealed a four-count indictment on June 25, 2025, charging West with conspiracy to commit computer intrusions, conspiracy to commit wire fraud, unauthorized access to protected computers, and wire fraud. Each wire fraud count carries a maximum sentence of 20 years. West remains in French custody pending US extradition proceedings. [20] 
Figure 7: FBI seizure banner displayed on BreachForums following law enforcement
action.
8.4 Key Lessons
|
|
[DFIR]
Abby Stract

Incident Responder
ASTRO
Posts:276
Threads:52
Reputation:59
|
Given that 44% of incident response cases now involve IAB-provided access and the median time from initial access to ransomware deployment is just 5 days, organizations must implement both preventive measures and detective capabilities that exploit the critical window before access is sold or used. [2,4,17] 9.1 Preventive Controls
9.2 Detective ControlsThe 5-day median dwell time creates a critical detection window:
9.3 Response CapabilitiesRapid response during the 5-day window can prevent catastrophic outcomes. Organizations need:
9.4 CIS Critical Security Controls Alignment
|
|
[Analyst]
Anna Lies

Market Analyst
ASTRO
Posts:312
Threads:67
Reputation:54
|
10.1 Quantified Impact
10.2 Estimated Financial Losses[5,14,17,25,26]
10.3 Emerging ThreatsSeveral trends will shape IAB operations through 2026:
|
|
[OSINT]
Dr. Detector

OSINT Analyst
ASTRO
Posts:189
Threads:38
Reputation:62
|
11.1 Recent DisruptionsBreachForums Timeline:
These actions demonstrate improving law enforcement capabilities, particularly in cryptocurrency tracing and international coordination. However, ecosystem resilience limits lasting impact: BreachForums returned after each takedown, IAB activity normalized within weeks of high-profile arrests, and the decentralized nature of the market means other operators quickly fill vacuums. [20,22,31] 11.2 Policy Recommendations
|
|
[Staff]
Sherlog Holmes

Researcher
ASTRO
Posts:847
Threads:156
Reputation:88
|
12.1 The IAB Threat in ContextInitial Access Brokers have evolved from niche service providers into a key foundational piece of infrastructure for the ransomware economy. The core metrics are clear: 44% of incident response cases involve IAB-provided access [2], a $6.3 million direct market enables $57 billion in downstream damage [5,14], and a median 5-day window from compromise to ransomware deployment [4,17] defines a threat that is both economically rational for attackers and operationally devastating for victims. Three characteristics make this threat persistent. First, professionalized bundled offerings mean ransomware operators receive attack blueprints rather than raw access. Second, the ecosystem demonstrates structural resilience from marketplace takedowns as individual arrests create only temporary disruption. Third, the shift to credential-based access renders perimeter-focused security insufficient against adversaries who authenticate as legitimate users. The cold open of this paper, ToyMaker's three weeks of silence, is not an anomaly. It is the model. The three-week gap was a detection window that went unused. The signals were there. Organizations that build detection capabilities around the IAB operational pattern give themselves multiple opportunities to break the chain before ransomware ever becomes relevant. 12.2 Five Critical Actions
12.3 Call to ActionFor Organizations: The attack vectors are well understood, and defenses are mature, but the gap is implementation. Every day without universal MFA leaves the dominant attack vector unaddressed. Frame IAB defense in terms of financial materiality: prevention costs a fraction of the average $4.9 million incident. For Industry: Active participation in sector ISACs, contribution of IOCs, and consumption of shared intelligence should be standard practice. Support legislation requiring mandatory IAB incident reporting within 72 hours and MFA mandates in critical infrastructure sectors. For Policymakers: Mandate phishing-resistant MFA for critical infrastructure, expand CISA's Automated Indicator Sharing program, establish legal safe harbor for good-faith breach information sharing, and strengthen cryptocurrency exchange KYC requirements. Initial Access Brokers represent the fulcrum point in modern cyber threats, the critical juncture where defensive efforts yield maximum value. The analysis is clear, the defenses are proven, and the cost of delay far exceeds the cost of action. |
|
[Staff]
Sherlog Holmes

Researcher
ASTRO
Posts:847
Threads:156
Reputation:88
|
[1] Recorded Future, Insikt Group, New Ransomware Tactics to Watch Out For in 2026, 2026. [2] C. Hegde et al., 2025 Access Brokers Report, Rapid7 Labs, Aug. 12, 2025. [3] J. Leyden, "Cybercriminals Exploit Low-Cost Initial Access Broker Market," Infosecurity Magazine, Oct. 16, 2025. [4] Cyber Risk Leaders, "Rapid7 Q1 2025 Incident Response Findings," Jun. 9, 2025; Sophos, State of Ransomware 2025. [5] S. Morgan, Global Ransomware Damage Costs Predicted to Exceed $275 Billion by 2031, Cybersecurity Ventures, Apr. 2025. [6] Check Point Research, Initial Access Brokers Involved in More Attacks, Including on Critical Infrastructure, Dec. 8, 2025. [7] VikingCloud, 46 Ransomware Statistics and Trends Report 2026. [8] Cyble Research and Intelligence Labs, 10 New Ransomware Groups of 2025 & Threat Trends for 2026, Jan. 1, 2026. [9] Check Point Research, Cyber Security Trends for 2026, Check Point Software Technologies, 2026. [10] See [1]. Recorded Future, Insikt Group, New Ransomware Tactics to Watch Out For in 2026, Recorded Future Blog, 2026. [11] Globe Newswire, "Rapid7 Access Brokers Report: New Research Reveals Depth of Compromise," Aug. 12, 2025.[12] Palo Alto Networks Unit 42, GoldMelody's Hidden Chords: Initial Access Broker In-Memory IIS Modules Revealed, Jul. 8, 2025. [13] D. Lohrmann, "The Top 26 Security Predictions for 2026 (Part 2)," GovTech, Dec. 28, 2025. [14] CYJAX, Initial Access Broker Market 2024 In Review, Feb. 6, 2025. [15] Cyberint (Check Point), Initial Access Brokers Report 2025, Apr. 2025. [16] R. Lakshmanan, "Initial Access Brokers Shift Tactics, Selling More for Less," The Hacker News, Apr. 11, 2025. [17] Sophos, State of Ransomware 2025.
[18] LoginSoft, Initial Access Brokers: The Hidden Architects of Modern Cyberattacks, LoginSoft Blog, Jun. 9, 2025.
[19] DeepStrike, Ransomware Attack Statistics 2025, DeepStrike Threat Intelligence, 2025. [20] U.S. Department of Justice, SDNY, Serial Hacker 'IntelBroker' Charged For Causing $25 Million In Damages, Jun. 25, 2025. [21] Chainalysis, The IntelBroker Takedown: Following the Bitcoin Trail, Jul. 22, 2025. [22] E. Kovacs, "British Man Suspected of Being the Hacker IntelBroker Arrested, Charged," SecurityWeek, Jun. 26, 2025. [23] Picus Security, IntelBroker Unmasked — The Story of Hacker Kai Logan West, Jan. 20, 2026. [24] Cato Networks, Threat Actor Profile: IntelBroker, Jul. 16, 2025. [25] IBM Security, Cost of a Data Breach Report 2025. [26] Comparitech / Healthcare IT News, Ransomware Downtime Costs U.S. Healthcare Organizations $1.9M Daily, 2025. [27] Trellix, Advanced Research Center, 2025 Healthcare Cybersecurity Threat Intelligence Report. [28] Center for Internet Security, CIS Critical Security Controls v8, 2021 (updated 2024). [29] Europol, Internet Organised Crime Threat Assessment (IOCTA) 2024–2025, 2025. [30] Cybersecurity and Infrastructure Security Agency, Cyber Incident Reporting for Critical Infrastructure Act of 2022 (CIRCIA), CISA, 2022.[31] Federal Bureau of Investigation, BreachForums Seized, Mar. 2023 and Apr. 2025. [32] Barefoot Cyber, Cybersecurity Weekly Update: 26 January–2 February 2026. [33] J. Shier, H. Wood, and A. Gunn, "Nowhere, Man: The 2026 Active Adversary Report," Sophos, 2026. [34] CrowdStrike, "2025 Global Threat Report," February 2025. [35] Mandiant/Google Cloud, "M-Trends 2025: Data, Insights, and Recommendations From the Frontlines," April 2025. [36] J. Chen et al., "Introducing ToyMaker, an Initial Access Broker Working in Cahoots with Double Extortion Gangs," Cisco Talos Intelligence, April 23, 2025. |
|
[DFIR]
Abby Stract

Incident Responder
ASTRO
Posts:276
Threads:52
Reputation:59
|
Abstract modernizes security operations through a composable SIEM platform that is modular by design, AI by default. Where traditional SIEMs force organizations into monolithic architectures and runaway log costs, Abstract decouples ingestion from analytics, embeds threat intelligence inline, and gives detection engineering teams the control and coverage they actually need. Organizations adopt what they need—data pipelines, streaming detections, or the full platform—and scale at their own pace. ASTRO, the Abstract Security Threat Research Organization, is Abstract's dedicated threat research function. ASTRO publishes original research across the threat landscape from threat actor campaign tracking and CVE analysis to emerging attack techniques in cloud and hybrid environments. Recent work includes research into North Korea's Contagious Interview campaign targeting developers through IDE infection chains, critical vulnerability analysis of Cisco Secure Firewall Management Center, and lateral movement techniques abusing managed identities in cloud infrastructure. ASTRO also powers Abstract's proprietary threat intelligence feed, with active tracking of over 60 C2 frameworks and botnets including the IAB infrastructure documented in this report. See more ASTRO research at abstract.security |